Over couple of days I have been working quite a lot with queues and queue items in Blue Prism. Every Blue Prism queue can be marked as encrypted in System settings. I used AES256 symmetric-key encryption algorithm.

There are some details of queues and queue items in Control Room but there is no view which displays content of each queue item.
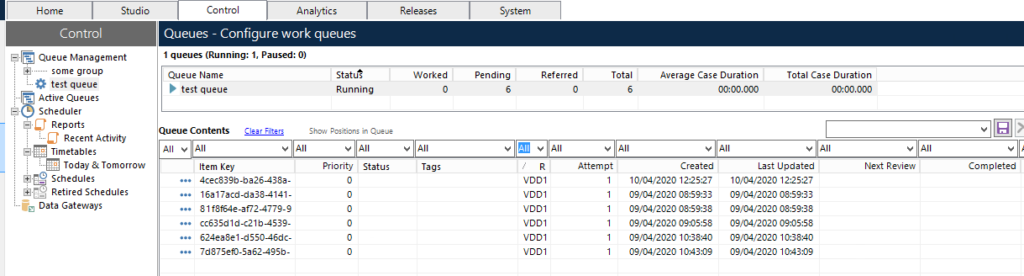
We may check what each queue item stores on database level .
select data from BPAWorkQueueItem;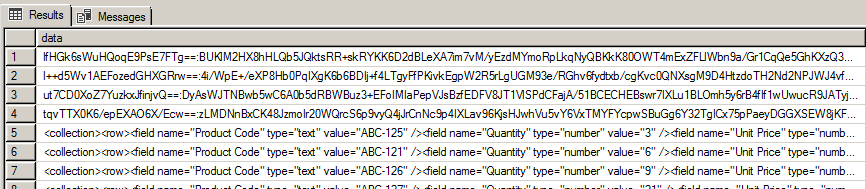
Queue item data is represented by single line xml. For non encrypted items it is e.g
<collection><row><field name="Product Code" type="text" value="ABC-125" /><field name="Quantity" type="number" value="3" /><field name="Unit Price" type="number" value="2.16" /><field name="Key" type="text" value="e8a4e2541033ab5248801b18616558e75a62fbc4b2096e964972767196afff4e" /><field name="Total Price" type="text" value="" /><field name="Order Number" type="text" value="" /></row></collection>After formatting
<collection>
<row>
<field name="Product Code" type="text" value="ABC-125"/>
<field name="Quantity" type="number" value="3"/>
<field name="Unit Price" type="number" value="2.16"/>
<field name="Key" type="text" value="e8a4e2541033ab5248801b18616558e75a62fbc4b2096e964972767196afff4e"/>
<field name="Total Price" type="text" value=""/>
<field name="Order Number" type="text" value=""/>
</row>
</collection>If queue item is encrypted then queue item stores some encrypted string
lfHGk6sWuHQoqE9PsE7FTg==:BUKlM2HX8hHLQb5JQktsRR+skRYKK6D2dBLeXA7im7vM/yEzdMYmoRpLkqNyQBKkK80OWT4mExZFLlWbn9a/Gr1CqQe5GhKXzQ3kt93LqWfAwtv5mS7WaNqdEy5Umi5gaZleaMaEm6cS//GmBQ1xW+mJDu5c/CVtp9c9blMr9PP/1Vw3m+aerFuBe4UXHyHm+3vlvqiFdyoJTc/TYjPIEWJEwPl3+JBvmBY848H1aLU437Ewq5BvoEUpqWehqAG0DH1UKDpeksfeK8El/LMgwVm87670qMRiEU4K8fHLwHhcU5NNxGlLYT4Gn0MqkwxP3IeMXB2E2l+aeRmGFVC7cwSQ+qIprbkvQTyb8A4T1356HtyDqRJRQomOje+VXpTIfZOt2hIwvra7/3l1+O8iTq+ioYAYrZr08QKxN/pjcuaEaPVZy54fCjhPg+uMbZVXWFgb/ttQxZgrHqD6TL7WP/uhPahEykn+xbADAL6NWcGUnfxoK3uc7Lv0Ar7NtZI8PdyfF9PcjW2boDoMkLG+Z4vbB1NRWI0QLPFFZvu9T/4=It consist of two parts separated by colon (:).
- Initialization vector – lfHGk6sWuHQoqE9PsE7FTg==
- Encrypted data – BUKlM2HX8hHLQb5JQktsRR+skRYKK6D2dBLe…
I was wondering how could I decrypt queue item data outside of Blue Prism. I did some research and wrote some code in Python which achieves it. First of all we need to get private key which is used for queue encryption. This key is not stored in database. It can be retrieved from Blue Prism server configuration
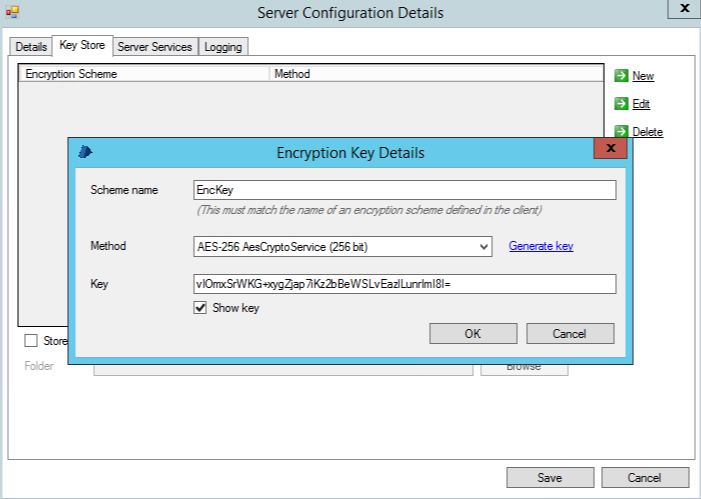
So let’s assume that we have this private key and want to decrypt queue item data.
import logging
from base64 import b64decode, b64encode
from Cryptodome.Cipher import AES
from Cryptodome.Util.Padding import pad
class BluePrismAes:
logger = logging.getLogger(__name__)
def __init__(self, credentials_key):
self.private_key = b64decode(credentials_key)
def decrypt(self, encrypted_string: str) -> str:
self.logger.info('Decrypting queue item data [%s]', encrypted_string)
encrypted_tab = encrypted_string.split(':')
iv = b64decode(encrypted_tab[0])
encrypted_data = b64decode(encrypted_tab[1])
cipher = AES.new(self.private_key, AES.MODE_CBC, iv)
return cipher.decrypt(encrypted_data).decode('utf-8').strip()I used pycryptodomex library for AES encryption. I wrote also unit test which checks if encryption works.
class TestBluePrismAes(TestCase):
logging.basicConfig(level=logging.DEBUG)
aes = BluePrismAes('LOm/OeAd4NpwKjA5CTgZGaRLqzXd0ii4a/IxYzYnGnY=')
def test_decrypt(self):
# given
with open('test/resources/security/encrypted_queue_item_data.txt') as res_file:
encrypted_item = res_file.read()
with open('test/resources/security/decrypted_queue_item_data.xml') as res_file:
expected_decrypted_data_item = res_file.read()
# when
result = self.aes.decrypt(encrypted_item)
# then
self.assertEqual(expected_decrypted_data_item, result)
Here is the code which encrypts data to queue item format
def encrypt(self, string_to_encrypt: str) -> str:
self.logger.info('Encrypting queue item data [%s]', string_to_encrypt)
cipher = AES.new(self.private_key, AES.MODE_CBC)
ct_bytes = cipher.encrypt(pad(string_to_encrypt.encode(), AES.block_size))
iv = b64encode(cipher.iv).decode('utf-8')
ct = b64encode(ct_bytes).decode('utf-8')
return f'{iv}:{ct}'All source codes can be downloaded from Github repository.